📌 Introduction
ARY‑PEN‑AI is not just a scanner — it is a new era of automated intelligence in defensive cybersecurity, ethical offensive testing, and professional bug bounty research. Built to analyze live websites, detect logic flaws, and give AI‑generated recommendations, it bridges the gap between traditional scanners and modern AI reasoning.
This documentary webpage walks you through the vision, evolution, and inner engineering of the project.
🚀 Vision Behind the Project
The cybersecurity world is evolving. Web applications now use dynamic JavaScript frameworks, async requests, token‑based auth, and complex logic flows. Legacy scanners fail to detect deep logic flaws.
ARY‑PEN‑AI was built to combine crawling, intelligence, and reasoning — bringing human‑like analysis to automated security testing.
🧠 Core Technology
ARY‑PEN‑AI supports:
- Google Gemini (Cloud AI)
- OpenAI GPT models
- Offline GGUF models via llama.cpp
- Full JS rendering with Selenium
- Deep recursive spidering
- Detection of XSS, SQLi, secrets, outdated libraries
The goal is to replicate what a professional security researcher does — but automatically, with AI precision.
📂 Evolution of ARY‑PEN‑AI
The project started as a simple Gemini‑powered source‑code analyzer. But after months of development, it transformed into a hybrid scanner capable of scanning forms, detecting misconfigurations, filtering domains using scope.txt, and generating structured reports.
🔥 Offensive Security & Bug Bounty Use‑Cases
ARY‑PEN‑AI is engineered with a **professional offensive-security workflow** in mind — inspired by tools from Kali Linux and OffSec. While the tool remains completely safe, it supports workflows commonly used in:
- Attack Surface Enumeration
- Reconnaissance‑style Automation
- Security Misconfiguration Analysis
- Logic Flaw Detection
- Adversarial Assessment for Hardening
- Bug Bounty Research Assistance
- Benign PoC Payload Creation
- Developer‑Oriented Vulnerability Insights
This makes ARY‑PEN‑AI highly useful for **ethical hackers, security researchers, and bug bounty hunters** who want AI‑assisted analysis without executing harmful exploits.
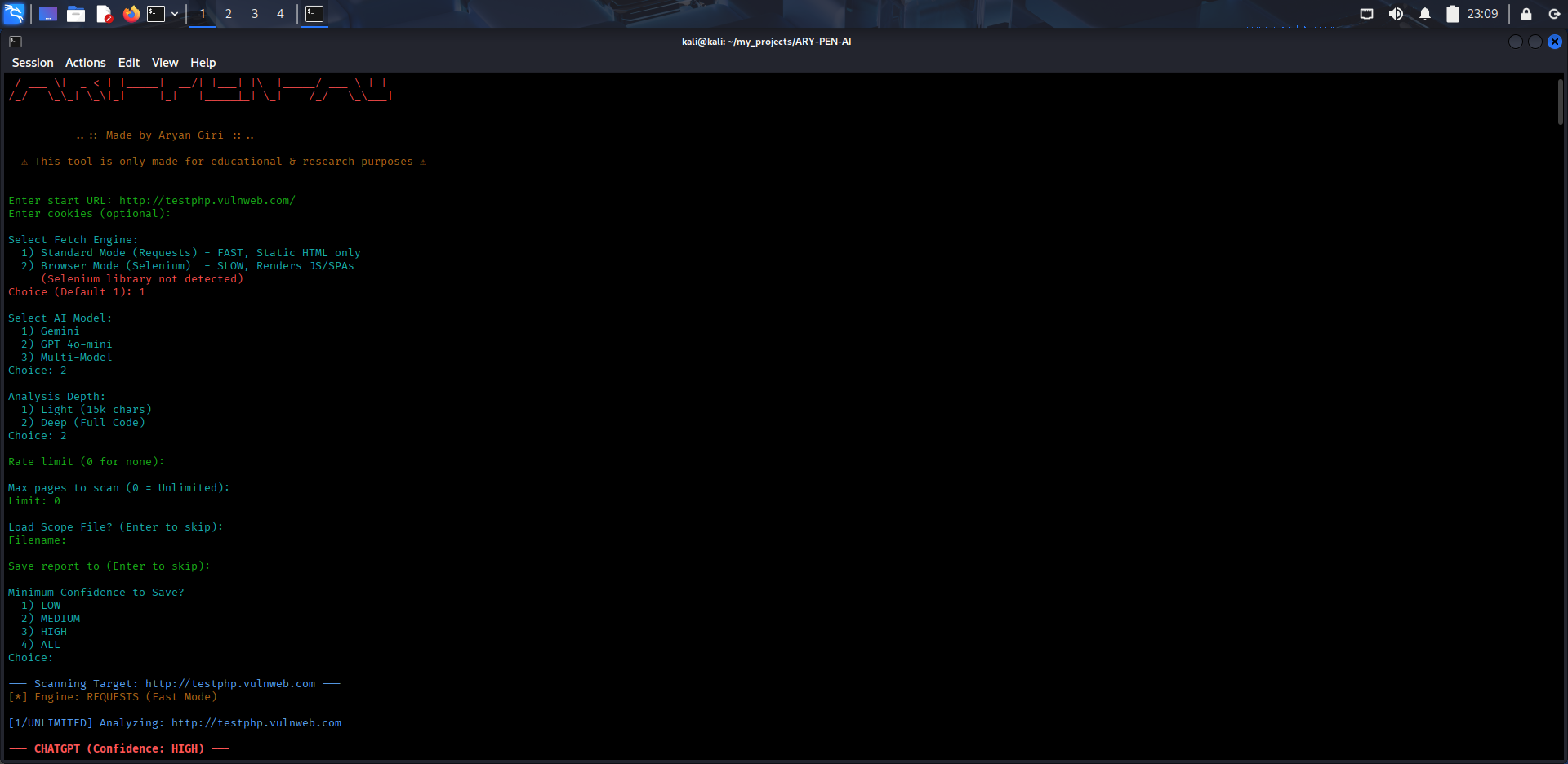
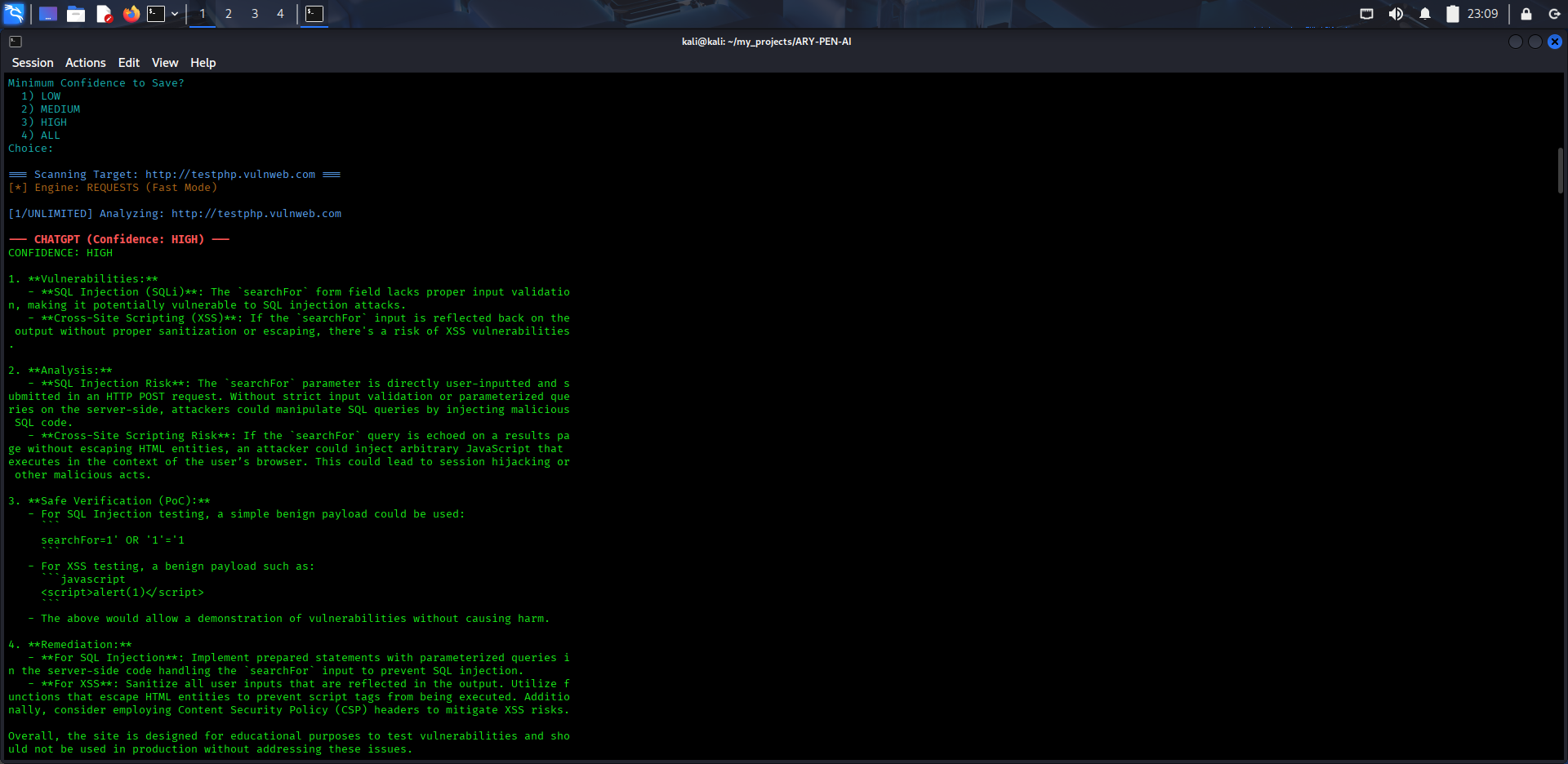
📸 Screenshots
🔗 Visit the GitHub Repository
Explore the full source code, updates, and documentation:
View Repository